Lab Walkthrough
The complete C++ source, PrepareStack.asm, and the dummy vulnerable driver are in the project repository: CVE-2025-8061. This content was inspired by Quarkslab’s article BYOVD to the next level
Welcome to a four-part deep dive into modern Windows kernel exploitation. In this series, we explore the Bring Your Own Vulnerable Driver (BYOVD) attack surface by dissecting and weaponizing CVE-2025-8061, a vulnerability found in a legitimate, signed Lenovo driver (LnvMSRIO.sys).
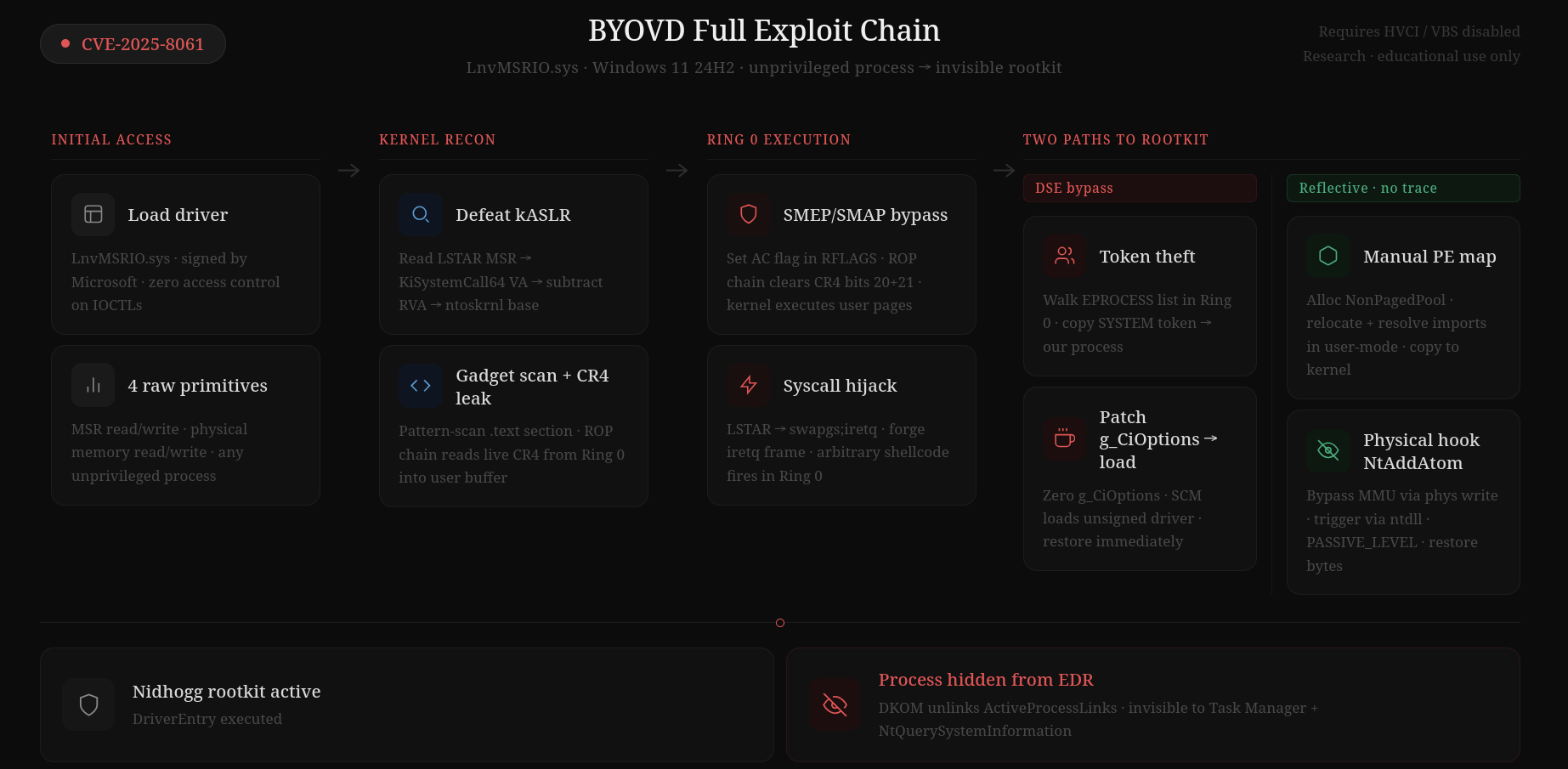
This series documents the complete evolution of an exploit, taking it from a fragile Proof of Concept to a stealthy, fully automated kernel implant:
- Part 1: We reverse-engineer the driver to extract arbitrary read/write primitives, defeat kASLR, and achieve initial Ring 0 execution to steal the SYSTEM token.
- Part 2: We rebuild the exploit for the real world. We strip away hardcoded offsets, introduce dynamic ROP gadget scanning, gracefully evade hardware mitigations (SMAP) using pure assembly, and implement cross-build structural dictionaries.
- Part 3: We move from privilege escalation to persistence and stealth. Using our stable Ring 0 execution, we dynamically blind Code Integrity (DSE), race PatchGuard, load an unsigned driver, and use Direct Kernel Object Manipulation (DKOM) to vanish our process from the operating system entirely.
- Part 4: We ignore DSE and load the driver reflectively, bypassing the standard windows driver loading process. We also go over the IRQL issue and move from running payloads with the LSTAR hijack to hooking a windows sys call function.
Understanding how attackers chain these primitives is the first step in building resilient defenses. Let’s dive in.